Values, Threats and Vulnerabilities Analysis
The module offers a way of structuring assessments and analyses associated with criminal and other undesirable acts and follows the Norwegian Standard for Security Risk Analyses NS5832:2014. The method is based on criminological theory, which identifies three factors that must be present and interact for a security problem to arise: values, threats, vulnerabilities.
The module presents a guide to, and descriptions of, the different stages in your analysis. In addition, the module enables you to communicate and store the results efficiently. This makes it easier to revise the analysis and keep it updated over time.
The Values, Threats and Vulnerabilities Analysis module in CIM requires some previous knowledge of this type of analysis, but the module assists you in the progress and structure of your work.
This module can be purchased as a single module installation, or it can be integrated into your existing CIM installation.
Values – Threats – Vulnerabilities
The module offers a way of structuring assessments and analyses associated with criminal and other undesirable acts, and the method is based on criminological theory, which identifies three factors that must be present and interact for a security problem to arise.
The method centres on the values assessment, stating that your values, not threats or vulnerabilities, must be the focus of any sensible use of security resources. If you have identified a value that you want to protect, you then must examine if there is a security context. A security context exists when we have something of value that we want to protect, there is something that threatens this value, and you see the need to implement measures to protect the value. If one of the three factors value, threat, or vulnerability is lacking, you do not have a security context. If this this the case, you are of course still free to use resources on protective measures, but it has no relation to security.
The method uses a social science approach – those involved in the process must use qualitative assessments. This in turn means that the results to a large degree are dependent on the data and information that are available at the time, and that these are interpreted correctly.
Another important aspect of this method is to highlight the complexity of the issues that are being analysed and to identify and reduce uncertainty in the data and the resulting assessments.
The method helps you present risks in a neutral, more approachable way to decisionmakers, in that risks should not be defined by probability and consequences, but rather as the result of an amalgamation of the three separate value, threat and vulnerability assessments.
In other words, the Values, Threats and Vulnerabilities Analysis module is a tool specially adapted both to assess the security risks and help you get through the process, get results, and follow up on them in the future.
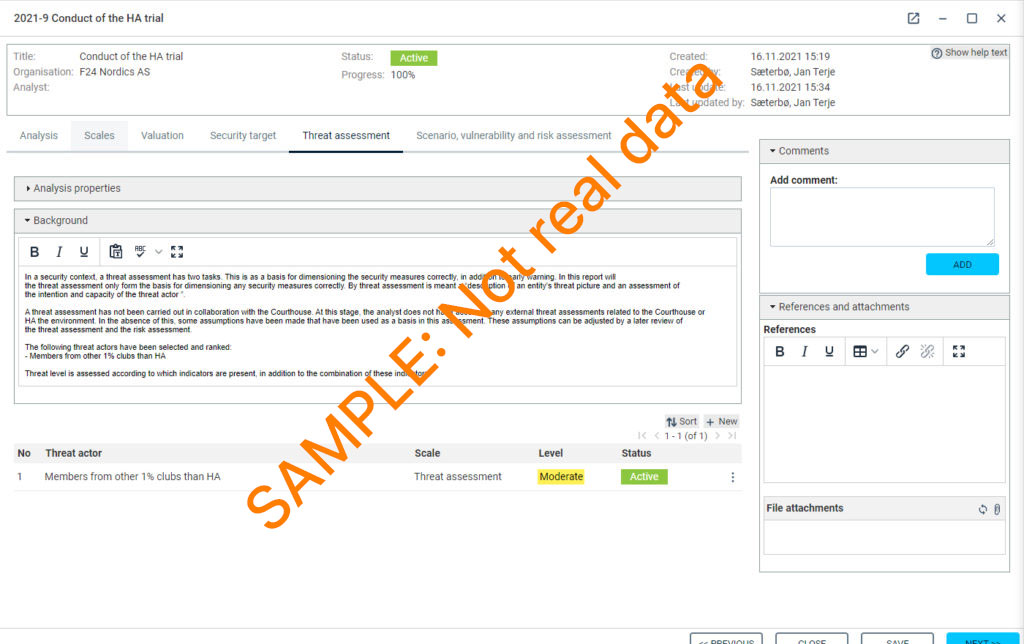
Sample pages:
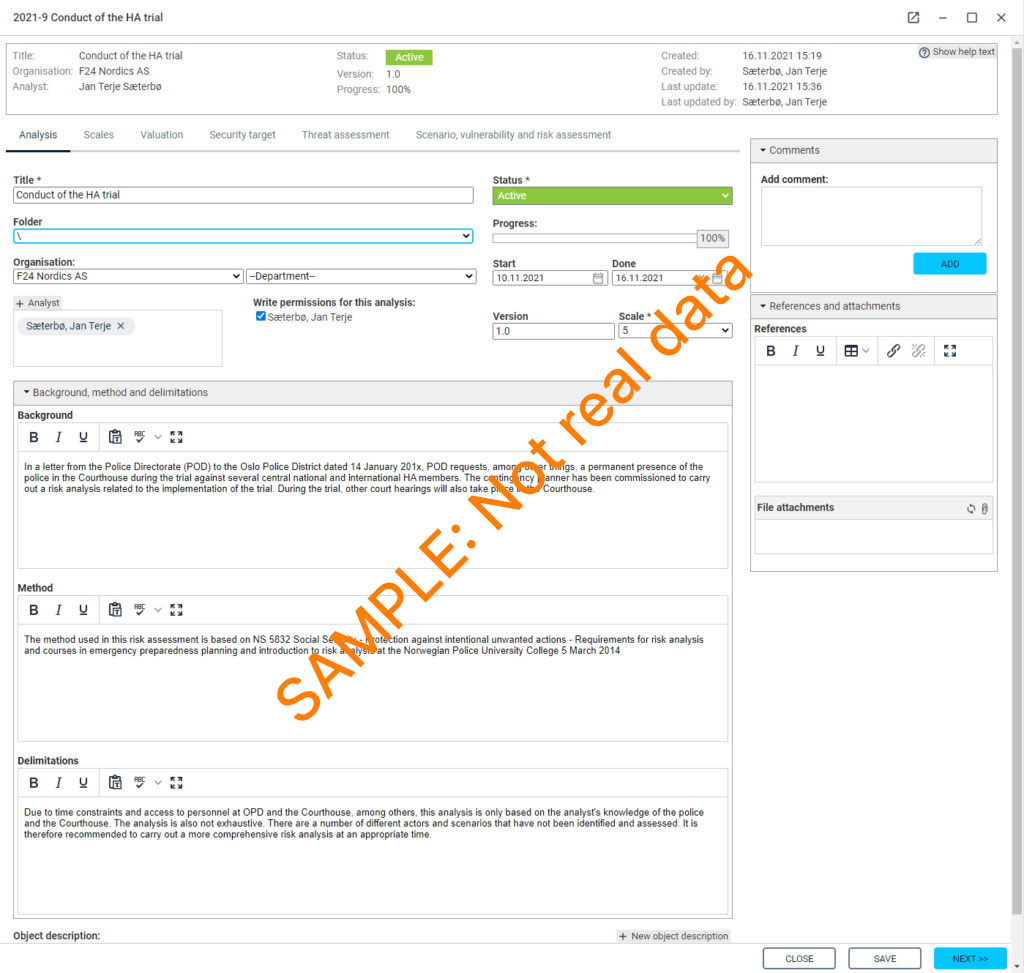
Analysis
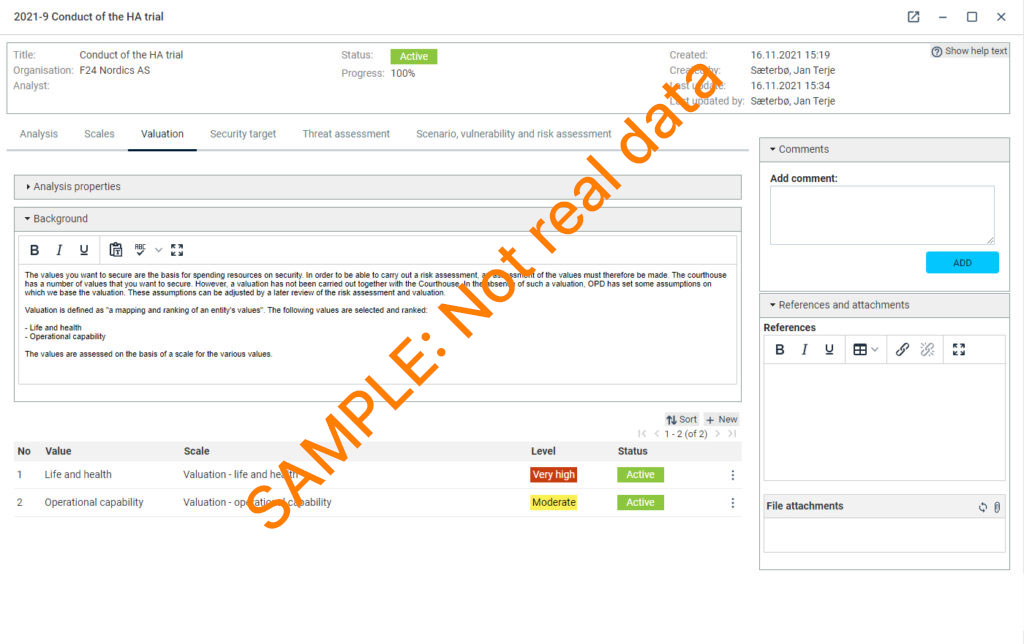
Valuation
Threat assessment
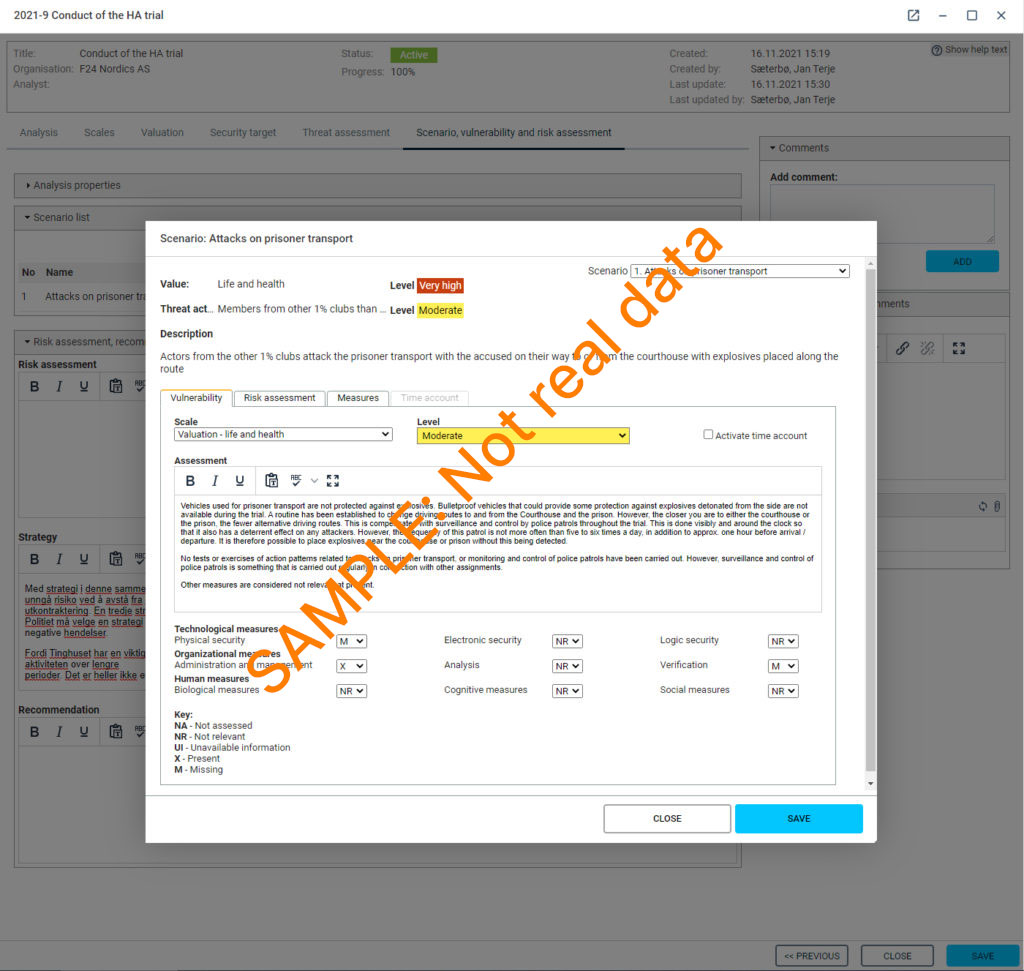
Scenario